Protecting 5G networks that will in many cases replace today’s Long-Term Evolution (LTE) technology will take a renewed effort to use cryptography at all levels: On the edge, to protect critical device and user information as well as the operations devices support; in the cloud where personal data and valuable business data will be stored; and in between the two, where encryption can keep data safe from prying eyes.
When done correctly, a commitment to security at all levels creates a fabric of trust between devices, users, networks, and operators.
As a way to examine changes needed on a global scale, let’s first examine today’s needs for secure storage and networking in machine-to-machine (M2M) devices running on LTE networks, which are already ballooning in much the same way 5G devices are expected to proliferate once next-generation networks are ready for large-scale rollout.
Building on Cat-M Device Security
In 2, 5, or 10 years, industrial and M2M use cases will only be one part of the mesh of connected devices operating in the 5G spectrum. In the next year or two, however, devices in factories, embedded in public infrastructure and used in healthcare or other high-pressure business settings, stand to be the first to gain from 5G’s ultra-reliable connectivity, low cost, and enormous data handling capabilities.
That’s because 5G will continue the trend of devices requiring less power, while providing reliable connectivity (when it’s needed). Today those ideals of low-power requirements and reliable connectivity are offered through newer LTE chip options like Cat-M (“M” for machines).
That makes today’s LTE Cat-M devices a decent analog for future 5G devices in terms of the technologies needed to protect them.
At the smallest level, Cat-M or 5G chips themselves have a big role to play in securing devices. These chips are secure elements where cryptographic keys can be held in quarantine, separated from the rest of the device. Those keys act as ID cards for networks—a device attempting to connect and send data to the cloud will need to match its key with the network key in order to be granted access.
The on-device key is also used to encrypt data before it’s transmitted to the cloud for processing and storage. Today’s Internet of Things (IoT) devices don’t collect or transmit much data all at once, but these properties of secure elements will be extremely important in 5G “edge” devices, which are expected to store some data and perform some data analysis and manipulation process on board.
Without strong encryption on board, the information stored on these edge devices will be at risk. Today’s IoT chips are designed to be functionally tamper proof—if the system senses evidence of device intrusion or attempts to penetrate the secure element, cryptographic keys can be zeroed to prevent a compromised device from connecting to the network.
As 5G devices proliferate, individual devices handling more data on the edge will be more valuable to hackers and could invite more attacks. Hopefully device makers will increasingly incorporate biometrics and other forms of digital identity authentication into their designs to reduce the risk of attackers gaining network access through a single end-point. But if attackers do gain access to a device, tamper-proof cryptography and the self-destructive capabilities of keys stored in secure elements are an important safeguard against network intrusion.
Scaling Security for Networks
Today’s 4G LTE networks are relatively centralized. Devices send data to a central processing environment, and that data is processed into usable insights, and sent back to the device for process optimization or for users to analyze.
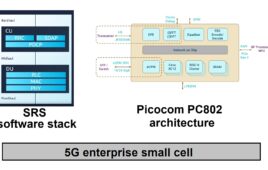
In 5G, networks will be more distributed thanks to network function virtualization (NFV), which (in part) will allow devices on the edge to perform typical network-level processes. NFV will also help companies move network functions out to the edge to realize cost savings, by reducing their need for network bandwidth, and for performance considerations by eliminating latency from data transmission.
As with massive deployments of IoT devices on LTE networks, companies building 5G networks will need to create a root of trust that can be extended through the entire network. At the network level, this is accomplished with hardware security modules (HSMs), which can be either secure hardware or virtualized processing environments.
These secure processing enclaves essentially act like giant secure elements, helping separate cryptographic processes from all other network activity and storing cryptographic keys for encryption, authentication, and network access. They should also be home to certificate authority (CA) processes, which create new cryptographic keys for devices being enrolled in the network.
As LTE networks have grown it’s become clear that these processes must be kept separate from normal data operations for two reasons: mixing cryptography in with database functions is inefficient, making enrollment, authentication, and updates slow and expensive. Furthermore, without a secure environment for these processes, it’s easier for hackers to use other data to reach cryptographic information and compromise networks.
Businesses that hope to deploy 5G IoT devices must use HSMs to protect their CA—the root of trust in their entire network. If an attacker could compromise the CA, they could potentially issue certificates to devices outside the business’ trusted network to steal processing power or data, or to take over networks by authenticating their way into existing edge devices.
Keeping Things Safe in Action
End-to-end encryption is the right answer to the attacks industrial and enterprise IoT networks face today, especially when devices are connected via WiFi rather than cellular. Unencrypted data transmissions allow hackers to collect data and inject their own to either infiltrate networks or seize control of devices.
In tandem with on-device encryption and tamper-resistant key infrastructure, encrypted data transmission will let 5G networks grow to replace today’s most critical LTE-M deployments first while beginning to create new, trusted connected platforms.
Industrial and infrastructure use cases are likely to be the first to benefit. Creating a fabric of trust through industrial networks—particularly in fields like military manufacturing—will allow factory IoT networks to apply analytics in real time.
Devices can collect and process data about manufacturing efficiency, resource availability, product stock and logistics and communicate with other devices on the network to slow or accelerate production. Securing communications between edge devices like sensors and control modules can help a network of several thousand devices operate and optimize themselves without risk of one compromised device shutting down production.
In the enterprise world, 5G will likely accelerate mobile business. Today, adding mobile devices to business networks without true end-to-end security can open doors for attackers. Building a fabric of trust and a robust key infrastructure from core networks to mobile devices will help 5G networks roll out more smoothly.
Better Security for Bigger Networks
Finally, while this article’s focus has mostly been on pure M2M edge devices, no discussion of 5G security would be complete without mention of vehicle-to-everything communications in our autonomous vehicle future.
Autonomous vehicles and smart infrastructure blur the lines between industrial and consumer networks. While consumers are the end users, businesses will manage the vehicles (edge devices) and the core networks that support them.
Creating a fabric of trust with HSMs at the core, encrypted data transmission between core networks and edge devices and with secure processing and storage elements in edge devices is the only way to ensure the safety of autonomous vehicles and the security of a newly connected infrastructure.
While attacks against enterprise and industrial networks can be damaging to businesses, the stakes are much higher on tomorrow’s roads. IoT innovators need to begin forging partnerships with security experts today to build a foundation for end-to-end trust in 4G LTE networks. The goal is to make it next-to-impossible and prohibitively expensive to direct attacks toward critical networks, and then extend that fabric of trust into the 5G era.