Fifth-generation wireless technology, or 5G, has been a hot topic among those in the telecommunications industry. Analysts expect this next industry wave to arrive by 2020, possibly even earlier. In spite of the widely-agreed upon timeline, operators shouldn’t wait until its arrival to prepare networks for the fastest cellular technology yet. After all, with the arrival of 5G and our increasingly connected world also come growing security threats.
So let’s break it down. What is 5G? What should we prepare for? And how can we arm ourselves against the growing security risks that come with anything that is more digital? This piece will break down the basics of 5G and what operators should know as we prepare for the impending arrival of the next wave of cellular technology.
What do the standards of 5G look like? What will be different about 5G than its 2, 3 and 4G sisters?
Throughout the history of mobile data, from early 2.5G onwards, data speeds have increased in many small steps within each generation of network. This will remain true for 5G. The real technological change will come about as a result of the need to support alternative uses.
To paint the picture, the original mobile use case was voice: calls last for a long time in computer terms – minutes rather than milliseconds. Bi-direction communications required roughly equal and relatively modest bandwidth in each direction, and delays in transmission of more than a few hundred milliseconds would cause problems. We then moved to an era of messaging: communication can withstand delays of minutes, bandwidth can be very low and uni-directional.
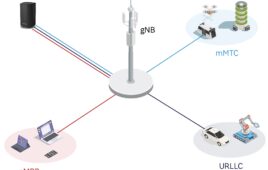
Today, however, the range of envisaged 5G use-cases each has its own needs for bandwidth, latency, transmission quality and variations of these over time. Take, for example, our reliance on applications like video on demand and video broadcast. Currently these use-cases still require traditional WiFi connectivity and reasonably fast Internet access. With 5G, however, these applications will be available on a mobile terminal.
It is expected that 5G technology will be able to serve billions of connected devices in a single network, addressing the growing IoT market where the amount of wireless sensors will explode in conjunction with real-time oriented applications. 5G is meant to minimize the latencies.
What’s the biggest challenge of 5G?
In my opinion, the biggest challenge of 5G is standardization. After all, it’s critical to ensure universal interoperability of this new technology.
5G use-cases will impact each of us in multiple areas of our lives—from education and healthcare to transportation and banking. While 5G technology will make these industries move technically forward, network operators will be challenged to make this technology commercially viable. This means ensuring that the cost of using the 5G mobile network enables rather than inhibits the use-case. With the vast range of use-cases, operators will need to define and manage many new commercial arrangements and pricing structures. The majority of the IoT use-cases will become realistic only at the moment that the required price tag can be achieved with the reality of volume production.
Is there anything operators should be wary about when it comes to 5G?
It’s important to note the technology of the mobile network core will be comparable (or virtually the same) with 5G as we’ve seen in previous generations of wireless technology. After all, network level signaling is the same in 5G as in the latest versions of 3G and 4G based on diameter signaling.
Diameter signaling vulnerabilities are comparable with the ones we have seen in 2G, expanding beyond the leveraging IP nature of the protocol. These risks will remain the same and require the same level of attention from security and core network teams. While having a decent protection on the radio level is critical, signaling still exposes location tracking, faking, spoofing, DoS and other types of attacks originated from 2G signaling principles.
It does not mean that mobile signaling protocols should be abandoned, however. It simply means that operators should take care not only of the IP based protection of their networks, but also of network signaling level security. This becomes extremely important in the light of rising IoT use-cases. An intruder into a smart traffic-control or a autonomously-driven car might lead to a total disaster if the attack is not detected and prevented in time.
Is there anything consumers can do to defend themselves and their products against security risks?
Consumers (generally) aren’t good at managing their own security. This is normally because we don’t necessarily understand the risk. How many of us download a new app and simply accept all the permissions it requests without really thinking about them? We freely give games access to our call history and contacts without a blink. We seem to trust that someone else is looking out for us. What consumers can do is look for a connectivity supplier that has built defenses in to their network.
The impending arrival of 5G was an ongoing discussion starter at Mobile World Congress. The conversation will only intensify as the International Telecommunications Union sets standards in place around 5G commercial deployments in the coming years. We’re preparing for it. Are you?
Ilia Abramov is a product director and security expert at Xura. Xura’s security solutions provide network-based security that protects the network and the customers it serves. The company ensures that the use of the network by customers is protected so that the services and consequent revenue are available for everyone.