Did you know the giant cranes at construction sites were vulnerable targets for cybercriminals? Federico Maggi and Marco Balduzzi were able to easily hack their way into various, large-scale industrial machines, putting themselves in command.
The two white hat hackers, who work for the Japanese cybersecurity company Trend Micro, made their way to 14 construction sites and asked if they could attempt to hack the machines, according to Forbes. It turns out, they were quite successful.
As described in an article by Trend Micro, the vulnerabilities were found in the machines’ radio frequency (RF) industrial remote controllers.
“The core of the problem lies in how, instead of depending on wireless, standard technologies, these industrial remote controllers rely on proprietary RF protocols, which are decades old and are primarily focused on safety at the expense of security. It wasn’t until the arrival of Industry 4.0, as well as the continuing adoption of the Industrial Internet of Things (IIoT), that industries began to acknowledge the pressing need for security,” according to the article.
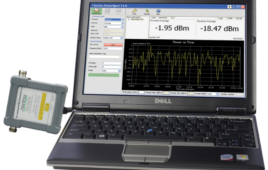
They were able to execute five different attacks: replay attack, command injection, e-stop abuse, malicious re-pairing, and malicious reprogramming and remote attack vectors. The first four attacks were so straightforward, they could be carried out within minutes at a low cost, according to Forbes. The two only needed a PC, free code, and some RF equipment that cost between $100 and $500.
To handle some of the construction tech’s more unusual features, they created RFQuack—a bespoke software and hardware solution.
Although these hackers were benevolent, the consequences of these weaknesses range “from theft and extortion to sabotage and injury,” according to the researchers in a paper.
To learn more about industrial machine vulnerabilities, you can read the study, “A Security Analysis of Radio Remote Controllers for Industrial Applications.”